This year brought what seem to be new developments related to cybersecurity in international relations. Arguably, the concerns tied to cybersecurity are not exactly new, but the current context is making it possible for policy makers and important stake holders to be more engaged with this issue.
The world today is obviously threatened by different actors than it used to be 60 years ago. Globalization, information technology developments, and the growing importance given to the “free”, “non-regulated” internet are shifting governments’ focus from traditional threats such as military concerns towards something else; wars can now be fought online, and extremely sensitive information can be accessed by highly-skilled, well-motivated private individuals while they are having their breakfast on the other side of the world.
What is cyber war?
Cyberwar is only one of the available methods used in information warfare in general, but probably the most dangerous. Julie Mehan makes a classification of the different types of cyberwar:
-
Class I, concerned with protecting/stealing private information; it is considered to be the “lowest grade” or the least harmful, although its results can also be devastating;
-
Class II is concerned with industrial and economic espionage; it can be directed against both nations and companies; the author argues that the number of perpetrations of this kind is on the rise;
-
Class III is a more serious offence and is about global war and terrorist activities, such as cyberterorrism; the range of activities employed here is large and they can target both an individual and a government;
-
Class IV is characterized as combining all the aforementioned techniques with the purpose of obtaining battlefield advantage; (2008: 27-28)
The US’ Department of Defense gives a more broader, yet more inclusive definition of cyber warfare:
An armed conflict conducted in whole or part by cyber means. Military operations conducted to deny an opposing force the effective use of cyberspace systems and weapons in a conflict. It includes cyber attack, cyber defense, and cyber enabling actions.
In the current context, there is a push for more regulation of the virtual world, while cyberterrorism has become quite the usual topic in the media. A very popular example can be given by the revelations made by Edward Snowden, a former US government contractor who released a series of documents containing extremely sensitive information regarding secret surveillance activities conducted by the National Security Agency (NSA). Snowden was forced to flee the country and, after moving from Hawaii to Hong-Kong and then Russia, his whereabouts remain to this day unclear; Snowden became in the process, one of the most well-known people in the world.
Snowden’s actions had implications internationally. As it turns out, NSA had been tapping even into Chancellor Merkel’s phone, leader of one of the most important US allies. The case became a huge media scandal and quite a diplomatic embarrassment for the United States’ relationship with the EU. The bilateral developments between the EU and China regarding cybersecurity are also interesting. China is somewhat feared in Europe for being a “bad guy” due to its failed attempts at protecting copyrights of EU companies. EU is an interesting case because there is a rift, a crack in EU-US relations, in general, since the 2003 French-German refusal to back the US in Iraq. China is seeing in this context a window of opportunity.
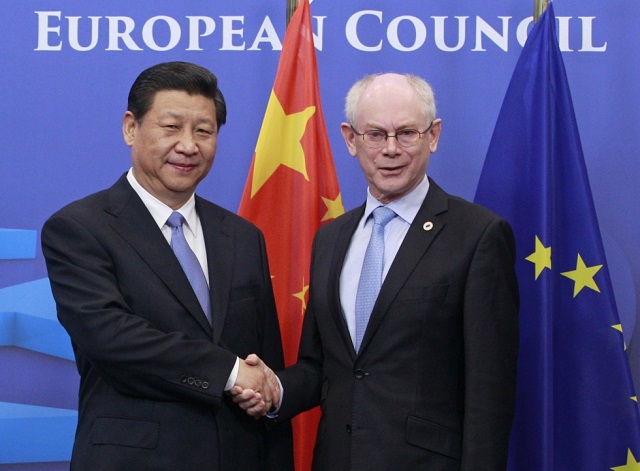
This year was important for the Sino-European relations. The two sides agreed that they should restart their bilateral ties and the world has seen president Xi Jinping doing a European tour in April, tour in which the issue of cybersecurity was a hot topic. The visit was not without policy repercussions, both sides publishing foreign policy documents designed to map out their relationship for the next 5 to 10 years.
However, EU’s relationship with China must consider the US’ take on the matter as well. Earlier this year, the Justice Department indicted some members of a Chinese military unit on the basis of stealing trade secrets from various American companies. This is extremely important, since it is the first time when the US poses such charges against a foreign country; the action comes at a time when estimates show that China will become the world’s first economy by the end of this year. Beijing denied the accusations, and it is unlikely that the five persons will ever see a US courtroom. However, we must ask ourselves if the US can afford to endanger its already shaky relations with China in this fashion:
-
Cybersecurity is important for the United States as well, and these developments show that Washington isn’t going to sit idly by; the willingness of EU and China to strengthen their co-operation on cybersecurity pushes the US to take a stance before it is too late, especially after the NSA fiasco;
-
The US’ decision to indict members of the Chinese military can be read as a response to EU’s own willingness to strengthen its ties with China; already weary of the Chinese intentions of drawing the EU closer in the pursuit of counter-balancing Washington, the US is now choosing the second-best course of action available: to at least side against China’s perpetrations (taking into account the NSA scandal, a reconciliation with the EU on cybersecurity would be either too early right now, or difficult to attain).
In more general terms, while agreeing that cybersecurity is indeed a problem, China sees itself as the victim, not as the perpetrator. China’s National Computer Network Emergency Response Coordination Center (CNCERT) published a report in 2012 showing that, regardless of the defensive measures taken by the authorities, China is still the biggest victim of cyber-attacks in the world, these attacks arising mostly from Japan, the US, and South Korea. This cannot surprise us. As we have seen in the recent case of the US indictments, the Chinese government takes very defensive positions when such accusations are made and tries to elude responsibility for investigating and catching the criminals.
As shown before, president Xi Jinping’s visit to Europe earlier this year was accompanied by a policy paper drafted by the Chinese Ministry of Foreign Affairs. Entitled quite pompously China’s Policy Paper on the EU: Deepen the China-EU Comprehensive Strategic Partnership for Mutual Benefit and Win-win Cooperation, the document does make specific references to the Chinese intentions in its cybersecurity relations with the EU. The reference continues along the same flowery writing style, but emphasizes the need of working together with the EU in fighting cyber-crime, in creating emergency response mechanisms, and refreshing the China-EU Cyber Taskforce, which has not been the most effective body, but has definitely helped reduce the mistrust between the two.
The EU, in its own cybersecurity strategy paper, outlines “drastically reducing cybercrime” as its second strategic priority. However, this could prove tricky to do. Member states such as France and Germany have other kind of fears regarding cybercrime: intellectual property theft which usually -albeit not exclusively- is initiated by Chinese individuals and/or companies. Therefore, we must ask ourselves whether China is indeed ready to find and prosecute intellectual property thieves active on their territory whom are helping Chinese companies become more competitive on the world market (albeit through illegal means).
When bringing the issue of human rights into the spotlight, things get even more complicated. China’s human rights record has been a delicate topic between the two for a long time now, but it increased in importance at the same pace with China’s economy and political role in international relations. The push for more and more freedoms in China was definitely not Beijing’s preferred approach; it surely set back the cooperation process between the two although one can see a good reason for this – the EU cannot (or does not want to) associate itself with illiberal states, with a less-than-clean human rights record.
Coming back to the cybersecurity discussion, we can find another point of divergence, stemming from the EU’s view about how the online space should be regulated. Maybe for a simpler process, or for trying to avoid an inflation of human rights conventions, the EU asks that “the legal obligations enshrined in the International Covenant on Civil and Political Rights […] should be also respected online.”
This complicates the situation for China even further. Even if Beijing was willing to cooperate on such themes, it probably wants to do it on their own terms, and they would like to have some maneuver room for applying the principles they had agreed upon. China is already rejecting applying the “Western” basic human rights to its offline, regular environment, so applying them to sensitive areas such as cybersecurity seems far-fetched.
It is therefore difficult to believe that the two governments’ views will somehow miraculously converge on the implementation in actual law of the principles and set objectives.
Some concluding remarks
However, these developments can also be seen as a step forward, since China has not issued similar policy documents for other important players and their main trading partners: the United States, Russia, nor Japan. This shows that China is also thinking in geopolitical terms – the EU being a civilian power, which does not pose military, sovereign, or territorial threats to it.
On the EU’s part, China’s criticism that it is incapable of acting as an individual, self-standing entity might prove to be true. Getting 28 states to agree on this issue is one thing, but getting them all to accept the Chinese terms as well is different discussion. Therefore, if the cooperation initiative is bound to fail, it may not only be due to Chinese reluctance, but also due to European divergence – as already discussed, Germany and France have very specific concerns about their cyber relationship with China.
If history is of any indication, warm relations between EU and China are not bound to last for too long. The cooperation procedure has serious hurdles to jump, such as differences regarding the human rights records, implementing the decisions agreed upon, and making sure that future perpetrations are dealt with, not to mention EU’s slow foreign policy decisional process.
When considering the geopolitical implications, China’s calculations may be wrong once again. By trying to speculate the crack in EU-US relations since the NSA scandal, China may overplay its hand; the EU and the US have been allies for decades and still share the same pattern of liberal values, while China is strongly clinging to its “Asian values”, incompatible with EU’s standards.
Even more so, the US seems that it is motivated to clear its name after the NSA fiasco; the indictment of Chinese military members for cyber-espionage is a serious signal for this. Mending fences with the EU may prove a difficult endeavor, but if there is somebody who can do it, it is probably the US.
Taking all these considerations into account, an optimistic view of these developments may not be recommended. Until both sides are ready for more serious concessions, in terms of unified foreign policy (EU) and human rights record (China), the latest Sino-EU developments in the field of cybersecurity are more talk than cooperation.